IoT Attack Sparks Warnings from Law Enforcement
ST Provides Tools Needed to Implement Recommendations of FBI and Other Agencies
The Internet of Things represents the next stage of the Web’s evolution. It is rapidly bringing to familiar devices—kitchen appliances, home cameras, residential security systems and the like—the same interconnectivity that computer users have been enjoying for many years. This connectivity is bringing an exciting new level of convenience and efficiency; imagine being able to look in on the kids via your smartphone from the office, checking the contents of the fridge before you leave work, to see what you might need from the store; or adjust the temperature of your home to suit your comfort.
Unfortunately, with its increasing adoption, we’re learning that the Internet of Things also represents the next generation of security threats. By definition, every IoT device needs some amount of computing capability; it also needs to be connected to the Net. Hackers have been able to take advantage of these two attributes to turn some IoT devices into foot soldiers in the latest wave of malware attacks.
The most dramatic example of this occurred in October, when the sites for CNN, Netflix and Twitter, among 80 million others, went offline. It emerged that they had been the subject of a Denial of Service attack on a scale never before seen. This occurred when hackers took advantage of the fact that many IoT devices come equipped with default passwords that most users never change. Find such a device, which is easy to do with automated Web scanning tools, and you can log in, take control, and get the device to do almost anything you want it to.
In the case of the October attack, the hackers installed a piece of malevolent software known as “Mirai” that took over control of the device and added them to a collection of tens of thousands similarly infected units, all part of a “botnet” that could be controlled by a single user. The Mirai botnet flooded the Web with terabytes of useless data. It was so much data that many sites were unable to maintain normal operations, at least not until engineers concluded a massive clean-up operation. Webcams are ideal for this sort of data-intensive tsunami, because of the high bit rates associated with video.
The October attack, while inconveniencing countless users, had two useful side effects. First, it demonstrated to IoT vendors that they could no longer consider security an afterthought, and had to be mindful of it from the moment they first begin to design their products, in the same way software makers learned to do long ago. Second, it attracted the attention of law enforcement, which quickly sprung into action with guidelines intended to prevent a repeat of this new breed of IoT Denial of Service outages. After Mirai, the FBI, the Department of Homeland Security and the National Institute of Standards and Technology (NIST) all weighed in with a checklist of best practices to keep the IoT safe.
The variety and breadth of IoT applications and devices, and their range of constraints suggests several security implementations of those best practices. The best practices recommend considering security threats in designing the IOT device to use the most relevant and cost-effective approach.
These recommendations can be implemented by vendors via the suite of security-related products from STMicroelectronics and others. For example, ST’s new STSAFE-A100 is essentially a design plug-in that secures communications and provides built-in authentication, key provisioning, and CC EAL5+ level security standards for IoT devices.
The responses from government agencies to the recent attacks were aimed at increasing vendors’ and IoT-developers’ awareness of the nature of the IoT security threat. The FBI, for example, issued a Private Industry Notification, that brought readers up-to-date on the crisis. It noted that computer security researchers have recently identified “dozens of new malware variants targeting Linux operating systems,” with those systems being a target because of their popularity in the IoT world. “Most of the Linux malware variants scan the Internet for IoT devices that accept Telnet, which is used to log into a device remotely, and try to connect to vulnerable devices by using brute force attacks with common default login credentials.”
 Once that is accomplished, the FBI said, the computer can be added to a “botnet” collection of similarly-hacked devices, which troublemakers can then use to target web sites. The attacks are likely to continue, the bureau said, “due to the open availability of the malware source codes for targeting IoT devices and insufficient IoT device security.” There are no confirmed suspects in the attacks, the FBI reported.
Once that is accomplished, the FBI said, the computer can be added to a “botnet” collection of similarly-hacked devices, which troublemakers can then use to target web sites. The attacks are likely to continue, the bureau said, “due to the open availability of the malware source codes for targeting IoT devices and insufficient IoT device security.” There are no confirmed suspects in the attacks, the FBI reported.
The FBI issued a number of recommendations, including that web sites develop a mitigation strategy ahead of time. For IOT device owners, it recommended disabling some of the features used by the malware for the initial infection, especially the “Universal Plug and Play” and “remote management” options in a router. It also suggested that the ports used as vectors of the recent attacks—23 and 2323—be either filtered or blocked by the system’s firewall.
For its part, the Department of Homeland Security issued a set of Six Strategic Principles for Securing the Internet of Things. The DHS paper told much the same story as the FBI’s, and was aimed mainly at vendors. The first principle was for IoT vendors to incorporate security at the design phase and suggested including hardware-based security in the design to strengthen the protection and the integrity of the device.
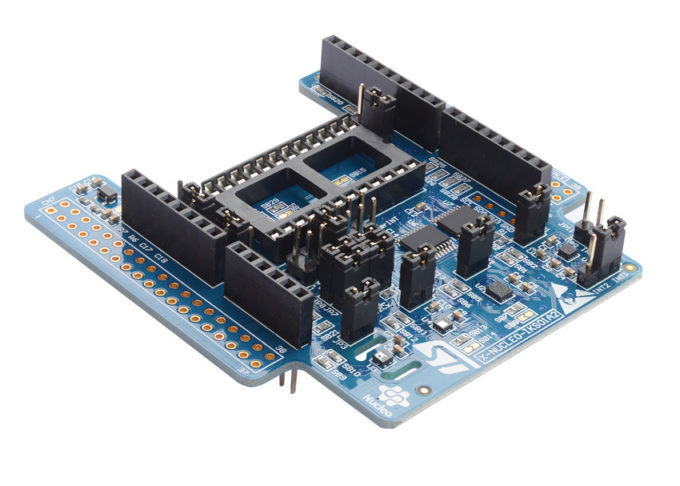
The STM32 Nucleo development platform.
That is exactly what the ST’s STSAFE-TPM Trusted Platform Module (TPM) from STMicroelectronics does. The STSAFE-TPM is a secure chip compliant with ISO/IEC 11889:2015 international and open standard developed by the Trusted Computing Group (TCG) organization.
The notion that security needs to be made paramount was a theme in the other five principles of the DHS paper as well. They included recommendations that companies build on proven security practices, and that connections be made to the Internet “carefully and deliberately.”
The NIST paper, “Systems Security Engineering: Considerations for a Multidisciplinary Approach in the Engineering of Trustworthy Secure Systems” was, at 242 pages, the longest and most technical of the lot. While released at the time of the Mirai news, the document had actually been in the works at the agency for four years. It describes some of the specific steps that engineers need to take to make sure that their IoT devices are as secure as possible and thus less susceptible to malware attacks. Or, in the words of the report, it’s a guide to “the engineering-driven perspective and actions necessary to develop more defensible and survivable systems, inclusive of the machine, physical, and human components that compose the systems and the capabilities and services delivered by those systems.”
A common theme in all three reports is that IoT vendors need to be vastly more mindful of security-related issues as they design their products. But owing to skill set issues, this has been easier said than done. For all of the engineering talent in house at IoT companies selling, for example, webcams, little of it is typically in the domain of security. That is where vendors like ST have begun to jump into the fray, playing an important role by providing turnkey security-related products like its STSAFE lines that allow OEMS to tackle the user features that represent their actual strength. And with a broad range of useful development tools, built around the powerful STM32 Nucleo development platform, prototyping, testing, and even test new applications for security vulnerabilities is easier than ever.
These efforts need to ensure a safer and more secure IoT.



